Dymaptic releases Infomaptic: better feature reports for ArcGIS Online and Enterprise
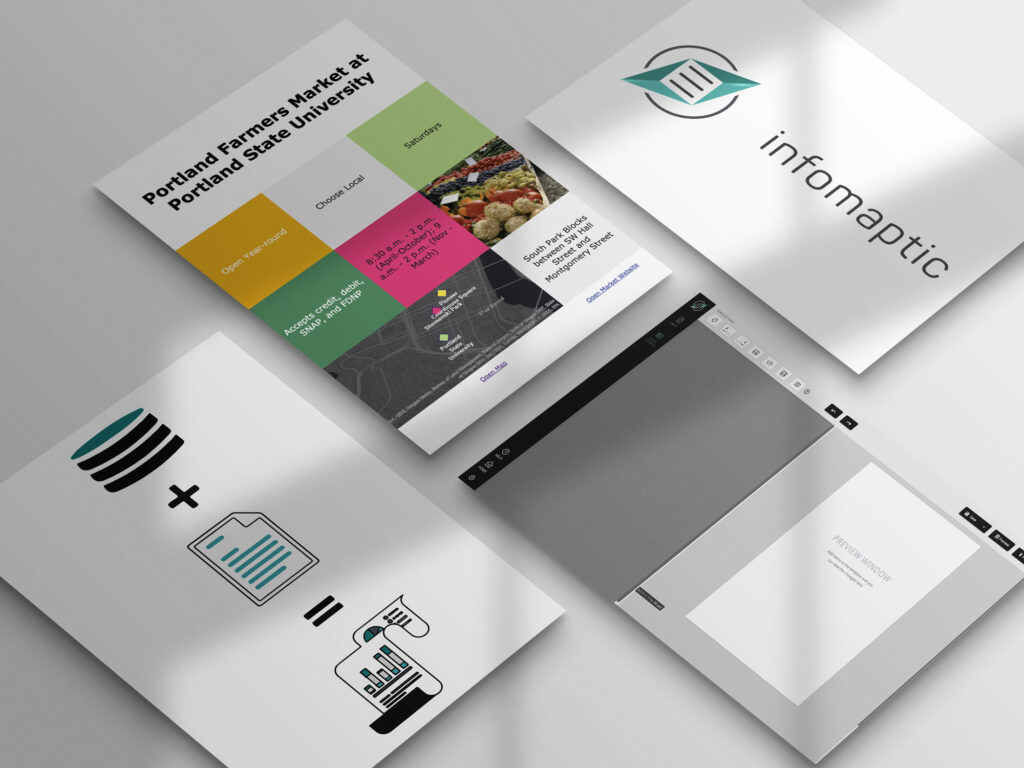
Dymaptic announces release of infomaptic, its beautiful new feature reporting app that integrates fully and seamlessly with ArcGIS Online and Enterprise.
Dymaptic releases Infomaptic: better feature reports for ArcGIS Online and Enterprise Read More »